A Tale Of Two Simple Account Takeover

Security Engineer
Hi everyone, so a few months ago I got the invite from a Hackerone private program, the program has huge scope. So I started my recon process. Found a subdomain let say test.example.com (As it a private program so we will be using example.com instead of the original domain)
I found 2 account takeover on the same subdomain using 2 different endpoint
Account Takeover Using Password Reset Functionality
Account Takeover Using Privilege Escalation And IDOR
So let's start
Account Takeover Using Password Reset Functionality
So basically user initiated a password reset
after that, the password reset token looks like below
https://test.example.com/Admin/NewUser.aspx?id=ZABlAGUAcABhAGsAZABhAHMAMgA4ADgAQABnAG0AYQBpAGwALgBjAG8AbQA=
so as you can see the id parameter value is base64 encoded
so I decoded the id parameter value and I got d e e p a k d a s 2 8 8 @ g m a i l . c o m
so the id parameter was endcode with user email with one white space in between every character, so got the account takeover, validate the same with another email its worked like a charm
Account Takeover Using Privilege Escalation And IDOR
After the first issue resolved again I dig the subdomain for more critical issue
so as you can see there one directory called admin so I started directory brute forcing
I found one file called /admin/abmhcpuser.aspx with 200 OK status code
by browsing the URL I got this
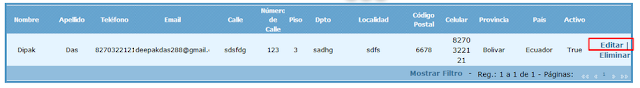
I was expecting to get the whole user but I saw there I can edit my own profile only 😥😥
so I decided to check the edit functionality for IDOR
So I changed the parameter value to my test account email and provided a new password in password parameter and forwarded the request, got 200 OK
edited my own profile captured the request found 2 parameter $wHCPUser$txtMedicEmail= and
`$wHCPUser$txtUserName=` the value was user email id, by default, the username set by the application was the user email id which you can't change
So I changed the parameter value to my test account email and provided a new password in password parameter and forwarded the request, got 200 OK
tried with the new password to login to my test account and I successfully logged in, I was like
Got some good bounty and bonus
Thanks for reading, any suggestion feedback are welcome
#s3gt_translate_tooltip_mini { display: none !important; }